Dr. David McGrogan’s recent article discussed the concept of Law 3.0, in which politicians try to use ‘smart’ technologies to make defying their demands not only illegal but impossible. In this article I consider how smart devices can be used in this manner, but also how protest and defiance by those made to endure smart technologies can again be made possible via a technical understanding of the technologies. However shallow, this understanding is still greater than that of most politicians subscribing to the Law 3.0 paradigm for the equipment their policies rely upon.
‘Smart’ might as well be an acronym for ‘Surveillance, Monitoring And Repression Technologies’; these days everything has to be smart. Smart speakers that report far more of your speech than just what follows their ‘wake word’ to remote corporate servers; smart home technologies which will lock up if you are (falsely) accused of racist language; smart meters which can be remotely switched to pre-payment mode; smart ‘security’ cameras which will hand over footage of the inside of your home to the police; smart phones which happily accept any software update the carrier pushes out; smart car companies which want to collect your genetic data (quite how they would achieve this remains questionable). You can get smart e-readers which will delete George Orwell’s 1984, and China uses smart locks to put all your comings and goings in to government databases. No, we can’t have good or reliable, instead it must be smart, that way the management at every manufacturer can feel a warm fuzzy glow from assisting in the implementation of Law 3.0, as Dr. McGrogan warned.
Sometimes a ‘golf cart’ analogy is used to describe the Law 3.0 paradigm. A golf course which doesn’t want people driving them across the greens decides to buy carts which will stop if they detect grass beneath them, rather than writing up a rule of “do not drive on the greens”. But the direction followed by the Law 3.0 paradigm does not match this analogy at all. Those golf carts are being restricted in their functionality, willingly, by the club which is buying them. They are restricted to serve the wishes of the buyer. But smart products, for the most part, are things you pay for, things which you probably do not want restricted and for which there are increasingly few non-smart competitors available.
Despite paying for them, in most of the ways which matter you have no true ownership over smart devices. A device reliant on a remote corporate server recognises that server, not the person who has paid for it, as the ultimate authority. If that server says “accept this update which will cripple your functionality”, it does. If the server says “start reporting extra telemetry back to us”, the device does. If the server says “our company is going bust, shut down forever” then an expensive gizmo becomes a useless brick. And it is entirely within the ability of this server controlled architecture to push a firmware update and start charging users rent for items they already, supposedly, own. Furthermore, in many cases if the device partially breaks, the ‘smart’ paradigm makes it impossible to fix by using DRM (Digital Rights Management – low level encrypted software designed to restrict user control) to refuse to function with replacement parts. Sometimes DRM takes the form of petty examples – a smart cat litter device for example – but the use of DRM is far more widespread and damaging. It is even built in to tractors and makes some of the modern models so dreadful to service that earlier versions now sell secondhand for higher prices than brand new vehicles.
If you cannot fully control a piece of equipment, and cannot repair it, you do not truly own it, however much you paid for it. Under any previous social system this would rightly be regarded as wrong, but under Law 3.0 the bug is a feature. Now you can be made to pay forever for things you should own. Now your devices can be deactivated by banks. Now your property serves a master who is all too keen to cave in to Government demands to surveil you, or to otherwise censor you.
There is however a slight glimmer of hope. Politicians and the managerial elite may demand these things, but they do not understand them. Watching Sir Humphrey, Jim Hacker and other political characters in ‘The Greasy Pole‘ all try to argue for and against a chemical plant, whilst doing everything they can to avoid admitting they know no chemistry, is an apt insight in to the career politician’s mindset.
No politician has ever tried to size the pullups on an I2C bus, trace a memory leak in C, or unlock a BIOS. Their profession looks to science as drunkards look to lamp-posts, for support, not illumination, and what gets sprayed around when they look to ‘The Science’ fits the drunkards and lamp-posts metaphor in a somewhat less palatable manner. They look to technology as something which will serve their will, but it doesn’t have to. Technology, in the end, obeys those who understand it best, those who can probe traces with logic analysers and read the secret DRM keys out of memory as a system turns on; those who can predict where an excessive quantity of bytes entered in to a data field will end up. Law 3.0 attempts to make ownership by purchase irrelevant, but smart devices cannot understand social structures and political hierarchies; when they are set up to serve ‘the state’ or ‘this corporation’ they can understand it only in terms of “serve anyone who can supply your root password”.
Restrictive corporate control over devices has long been a source of annoyance to the technical geek (sometimes described as hacker or maker) community, a community which has proven itself resourceful in overcoming them. The Law 3.0 paradigm can be closely linked to the concept of a “War on General Purpose Computing“, in which corporations seek to phase out user-controlled computing in favour of systems that will only perform approved tasks. Given the collusion for censorship between Big Tech companies and governments which has become common since those companies grew from small libertarian-minded startups, run by geeks at the coal face of technical development, into corporate behemoths in which most of the control lies with middle managers who can always be counted upon to approve of ‘the latest popular thing in Government’, it isn’t hard to imagine connections between Government and industry in this respect. Authoritarian governmental and corporate types would like to monopolise modern, computer-dependent technologies to only do as they wish, but the computing concept which underlies them, as in Alan Turing’s mathematical idea of processing numbers via a series of operations to produce other numbers which can cause meaningful outputs (turn on the LED, close the relay, put text on the screen etc.), is perhaps the most generalisable technological concept known to man. There is, fundamentally, no such thing as a computer that can only do X, and politicians are not at all happy about that truth. Computation in a specific device might be physically limited by how long a series of instructions can be provided, how many variables can be held in the memory at once, how long each instruction takes, or what input data and output capabilities it is physically connected to. But within those capabilities there is no computer than can only do things the way a Government or corporation wants it to. Authoritarians then resort to trying to mandate that communications be surveilled and censored and that malware and spyware be built in to devices in a way which uses some form of DRM to stop them being removed. That is to say, they get devices to treat the user as the enemy.
And when devices treat the user as the enemy, the ‘geek’ community doesn’t tolerate it. When DRM schemes treat the user as the enemy in a cryptographic sense, and try to hide secrets from them, those schemes attempt to maintain a delicate balance of placing the decryption key inside the device without it ever entering the user’s hands. Sooner or later this is always beaten, just like attempts to backdoor encryption with a golden key that ‘only the good guys’ can use, keys always get out somehow. Virtually all Law 3.0 supporting devices are built on the (inevitably incorrect) assumption that a device can decrypt a secret (after all, a device can’t follow secret instructions until it translates them into a state from which it can read them) without revealing that secret. I think we can safely say the only examples of DRM remaining unbroken, by one means or another, are where it is on devices so rarely found or unimportant that nobody from that community has seen fit to try beating it.
Another thing the community doesn’t tolerate is planned obsolescence. And with ever more devices becoming smart, being able to fix them ends up requiring the same techniques as defeating DRM. Once a device contains computing functionality, getting a broken one to work again has many technical similarities to getting a restricted one to behave freely. Part of this movement has taken to political activism, and has eventually achieved some success in doing so, with several jurisdictions now passing right-to-repair laws. But the core of the movement is those who opt not to worry about digital copyright implications and to plough ahead to fix devices regardless, treating the worst excesses of poor internal design and outright malicious internal design as obstacles to be overcome by technical means. It is on this core that the movement’s political successes have been able to ride. The tools which geeks develop to perform repairs and modifications this way get shared as open-source projects, for example the Flipper Zero, HackRF, or BusPirate, as do alternative pieces of software which can then run on repaired or modified smart devices. Free and Open Source Software Linux (GNU/Linux) distribution operating systems provide excellent alternatives to Windows for laptop, desktop and server computing, all the more vital when Microsoft shows itself to be not only woke but also seeks to remotely keep a copy of your key before you can enable disk encryption. And there are application specific projects like OpenWRT for routers, openHAB or Tasmota for home automation, Libreboot for low level BIOS replacement, and RockBox for mp3 players.
A key principle behind this open-sourced software is that it is ‘free’ in the sense that it ‘respects your freedom’ to use it, study its internals, modify it and further distribute it as you wish, not just ‘free’ in terms of price. As these projects are widely shared online, anyone with relatively basic technical skills can download and make use of at least some of their powerful capabilities. And repressive nations which wish to prevent their populations repairing or truly owning their own devices are powerless to stop them. They cannot seize at the border things which people can build for themselves from open-sourced instructions. Furthermore, the underlying code of an open-source project is out there for all to see. It is not hidden away inside a corporation who can quietly comply with governmental demands to introduce backdoors or other unwelcome ‘features’. Where corporations can be threatened with burdensome new regulations, code shared among people cannot be threatened even if some of the people are. Where corporations might, if particularly upstanding, pull out of a jurisdiction which demands immoral actions from them, open source projects keep running in open defiance of diktats. They couldn’t pull out even if they wanted to; once code is shared it almost takes on a life of its own. And where a Government tries to enforce bans on encrypted communications, the right sort of open-source code can always be used to produce methods for communication which are not only encrypted but steganographic. That is to say, not only is the user’s private message hidden, but so is the mere fact that they are sending a private message at all.
I will admit that far too many prominent figures in the geek, hacker, maker and right-to-repair community have fallen for much of ‘the Narrative’, and whilst I can’t fault anyone, who, in the confusion at the very start of the Covid pandemic thought printing face shield clips for nurses was a useful move, I definitely have concerns about those who thought mask detection machine vision cameras were a wise idea for a hobby project. Ventilators for Covid may have been worse than useless, often actively harmful, but making equipment work again when its manufacturer would rather it didn’t certainly shows talent. As for those who chose to spend their spare time devising open-sourced blueprints for SMS-calling accelerometer-based quarantine bleepers to stick on doors, some people clearly cannot imagine the dangers their talents can unleash. But this is the body of people we need to get onboard. In Ukraine these are the types of people finding ways to modify common commercial drones to assist their soldiers. What could be done with the same levels of determination and technical talent turned to undermining ‘smart’ surveillance and censorship? Free speech campaigning might not have much use for drones, but there must surely be technologies in existence or development that are as helpful to it, and unexpected in their usefulness, as drones have so quickly proven themselves to warfare.
It is all too easy for people with talent in developing and debugging software and hardware to find jobs in which they end up assisting the ambitions of politicians with authoritarian tendencies. Consider the number of programmers hired to develop the abominations which were vaccine passport apps. Our side of the debate needs to look for ways we can use these talents to increase individual liberty instead of corroding it. The types of people who love tinkering enough to do it in their spare time are the types of people we need, and one hope that folks who aren’t willing to let a distant corporate server tell them what they can and can’t do with their own property should hold Government demands in similarly low regard.
The threat posed to liberty by the concept of load-controlled appliances within the Energy Bill (which prompted Dr McGrogan’s Law 3.0 article) provides a topic for some speculation on what the community might achieve. Let’s start by considering what a load-controlled appliance does, and how it could do it. To receive load control signals it will either have to do so electrically, perhaps through Power Line Communication (PLC) data signals superimposed onto a mains AC waveform, or via a radio receiver. In the former case it could always be possible to electrically filter the power supply to suppress waveforms faster than 50Hz; the result would be no PLC signals reaching the appliance. In the latter an antenna must be fitted somewhere within the dishwasher, fridge or other piece of equipment. It would not be hard to recognise and remove that antenna. Even in a diabolical scenario where the appliance would require a constant valid signal to remain active, rather than being remotely switched off from a default operating condition by a signal from a load controller, a dummy signal could be locally supplied to keep the appliance running. If the load control signal used a form of DRM-style authentication on the signals to try to prevent ‘unauthorised’ users from operating their own devices as they see fit, the presence or lack of that load control signal would, inside the appliance, somewhere become a simple high or low logic signal being transferred along a circuit board trace between the chip that reads the reads and verifies the control signal and the chips actually responsible for making the appliance function. Even if the DRM was unbreakable, as every politician believes such things can be simply because they demand it and as every geek knows to be mathematically impossible, that simple ‘high for keep running, low to switch off’ signal further along within the device could be trivially spoofed instead. This is of course speculation about the nature of devices not yet produced, but the fundamental nature of what these appliances must do in their role as appliances suggest that if all else fails, removing the boards on which smart circuitry resides and replacing them with the ruggedised equivalent of an Arduino, and an appropriately isolated low voltage DC supply for it, to control a few relays would work.
Another point for speculation, though perhaps beyond the realm of the typical keyboard-bound hacker or electronics geek at his test bench and into the realms of garage tinkerers, is the threat of an electric car mandate. If cars are to be sold as electric, why need they stay that way? Replacing an electric drive train with a conventional transmission may be mechanically impossible for some designs of chassis, but an internal combustion engine powering an electric generator would give a lot more freedom in terms of locating it with a vehicle’s structure, and far superior driving range. That concept, plus a battery, already runs in hybrid cars, and diesel-electric transmissions have a long history of reliable operation for railway locomotives and boats. A tinkerer could make a lot of money with a startup from a shed selling an ‘electric’ car for which a readily swappable battery, undersized if it is to be cheap as after all nobody would actually use this battery, could be removed and a compatible internal combustion engine module hoisted in to its place, notionally by the buyer, seconds after the car’s sale had happened.
Even the simplest of technical realisations can defeat a system. The recognition that Ulez cameras were looking at the difference in infrared (rather than visible wavelength) reflectivity between the black lettering and a registration plate’s background (the clustering of LEDs around them makes this somewhat obvious in hindsight) has let people start selling thin films which, while transparent to visible light, cause the whole area of the plate to become equally reflective or absorbent to infrared, making it impossible for the cameras to read.
The more dystopian Law 3.0 possibilities become, the more coercion and control they involve, the more smart technologies they depend upon. The most chilling sort of vision just isn’t practical if authoritarians’ capacity for enforcement is limited by the availability of human manpower. And the more that Law 3.0 is relied upon by the political class, the fewer resources they will be able to invest into other methods of control and coercion, and the greater therefore become the opportunities for successfully undermining it. So remember, if you have any ideas about which aspects of Law 3.0 would be the most useful to circumvent, raise your voice, and maybe someone can work out how. And for anyone who finds out how, in the case of any specific system, open-source it and tell the world – the world will thank you. Law 3.0 might not be debated in the Commons, or defeated in court, but, like the parasitic thing it is, it can be damped out in-circuit.
Dr. R P completed a robotics PhD during the global over-reaction to Covid. He spends his time with one eye on an oscilloscope, one hand on a soldering iron and one ear waiting for the latest bad news. He wishes the free speech and anti-authoritarianism movements would frame the challenges facing us in such a way that folks with engineering skills might be able solve them, and wishes he had the skills necessary to solve all these challenges, not just contemplate them.
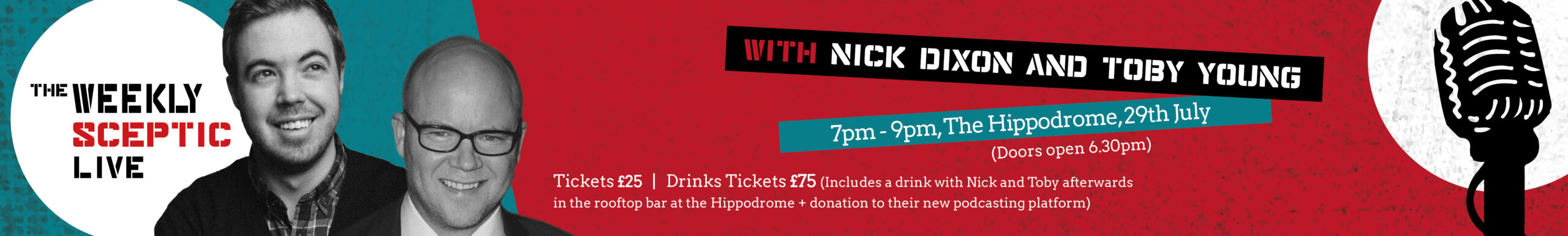










To join in with the discussion please make a donation to The Daily Sceptic.
Profanity and abuse will be removed and may lead to a permanent ban.